Rest Authentication Methods are a fun and engaging device for youngsters and adults, supplying a mix of education and enjoyment. From coloring web pages and problems to math challenges and word games, these worksheets cater to a vast array of passions and ages. They help improve critical thinking, analytic, and creativity, making them excellent for homeschooling, classrooms, or family members tasks.
Easily obtainable online, printable worksheets are a time-saving resource that can transform any kind of day right into a learning experience. Whether you require rainy-day tasks or additional understanding tools, these worksheets offer limitless opportunities for enjoyable and education and learning. Download and appreciate today!
Rest Authentication Methods
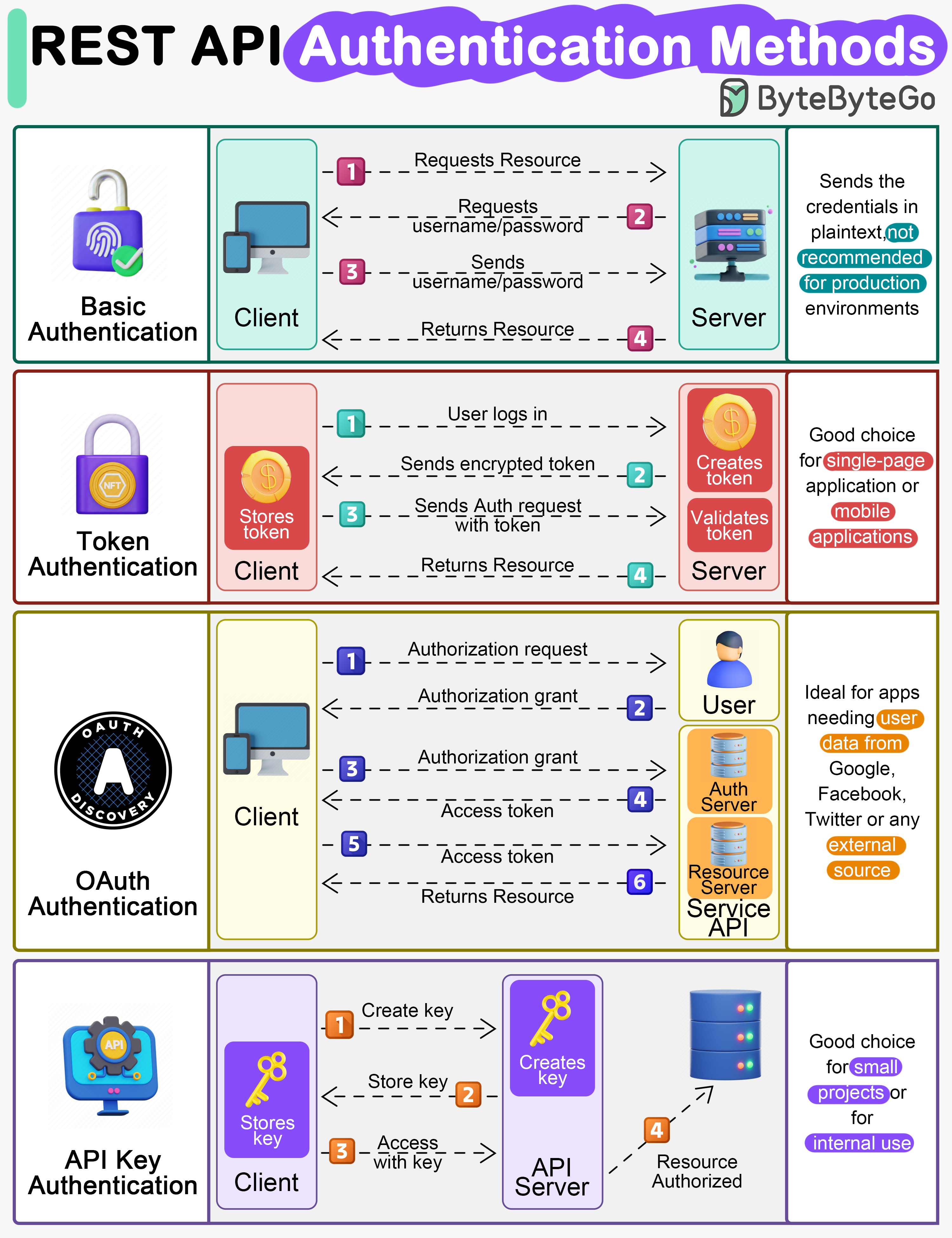
Rest Authentication Methods
Our printable second grade reading worksheets help seven and eight year olds practice compound word recognition pluralization reading comprehension and more This is a free sampler of 2nd Grade Fluency Homework. It contains 3 weeks of homework. There are 9 pages included in the sampler.
2nd grade reading Worksheets word lists and activities

Mikael Svens Medium
Rest Authentication MethodsApr 4, 2020 - Explore Epic Worksheets's board "free reading comprehension worksheets 2nd grade" on Pinterest. See more ideas about reading comprehension ... A series of Reading Comprehension Worksheets for second grade 2nd Grade Students read the passages and answer the questions that follow
Here is a collection of articles and stories written for students at a second-grade reading level. Each worksheet includes questions to help test your students' ... Images Of Metal API JapaneseClass jp EP91 REST API Authentication Methods
Second grade reading comprehension freebie TPT

Server Setup Para Docs
Short stories and poems followed by comprehension questions at a grade 2 level Fiction and non fiction texts up to 200 words long Free Reading Cheat Sheet For Designing Secure Systems
Free 2nd grade reading comprehension Passages 36 weeks printable PDF worksheets to use in the classroom or at home Click here Forward Proxy Vs Reverse Proxy Authentication Vs Authorization

REST API Authentication Methods Figma
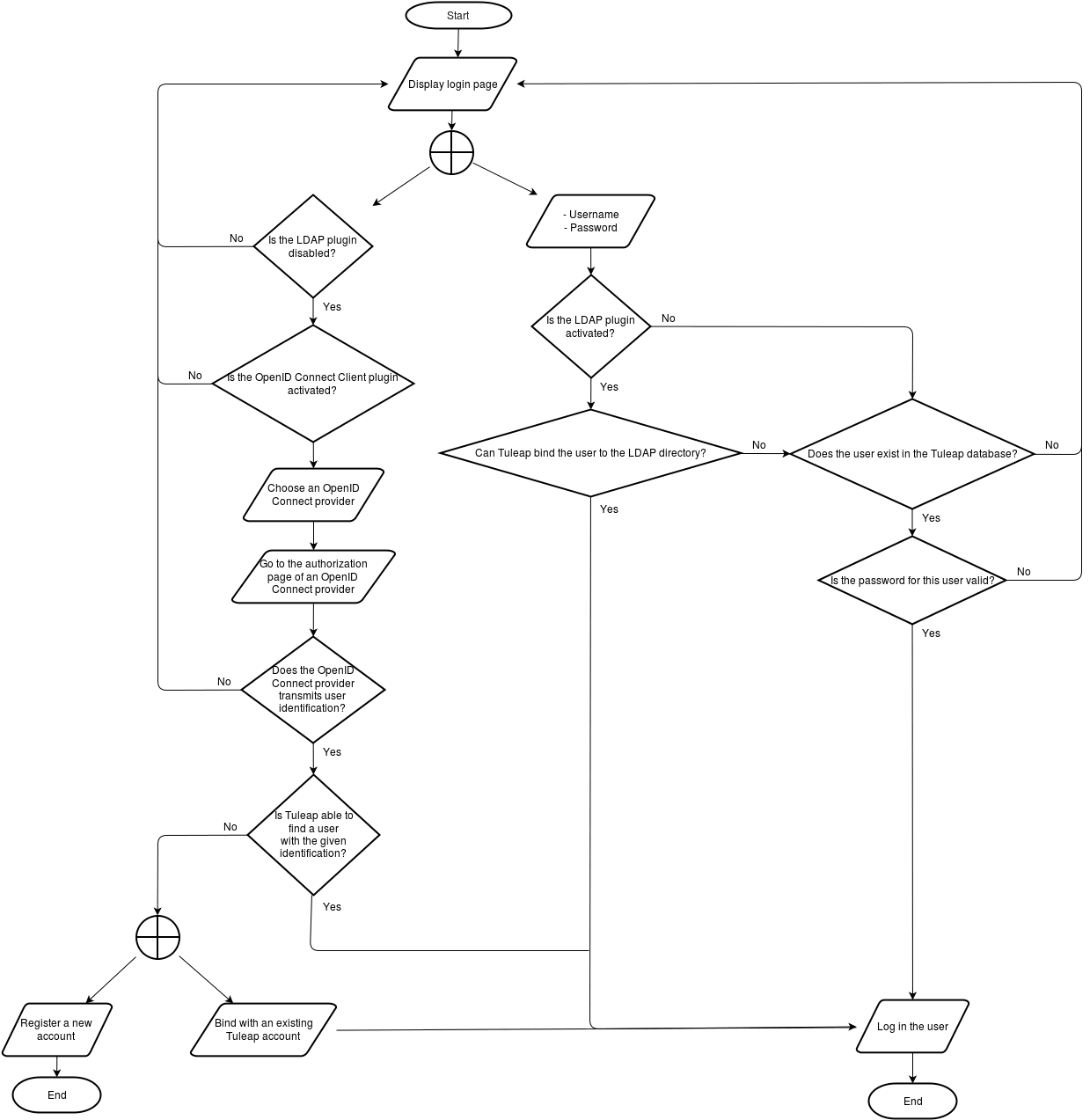
User Authentication Flowchart Tuleap Latest Version Documentation

Types Of Hackers
Types Of VPN
What Is DevSecOps

How Does SIEM Work
msc12 cybersecurity microsoft365 authentication Omar Kudovic
Cheat Sheet For Designing Secure Systems

EP91 REST API Authentication Methods
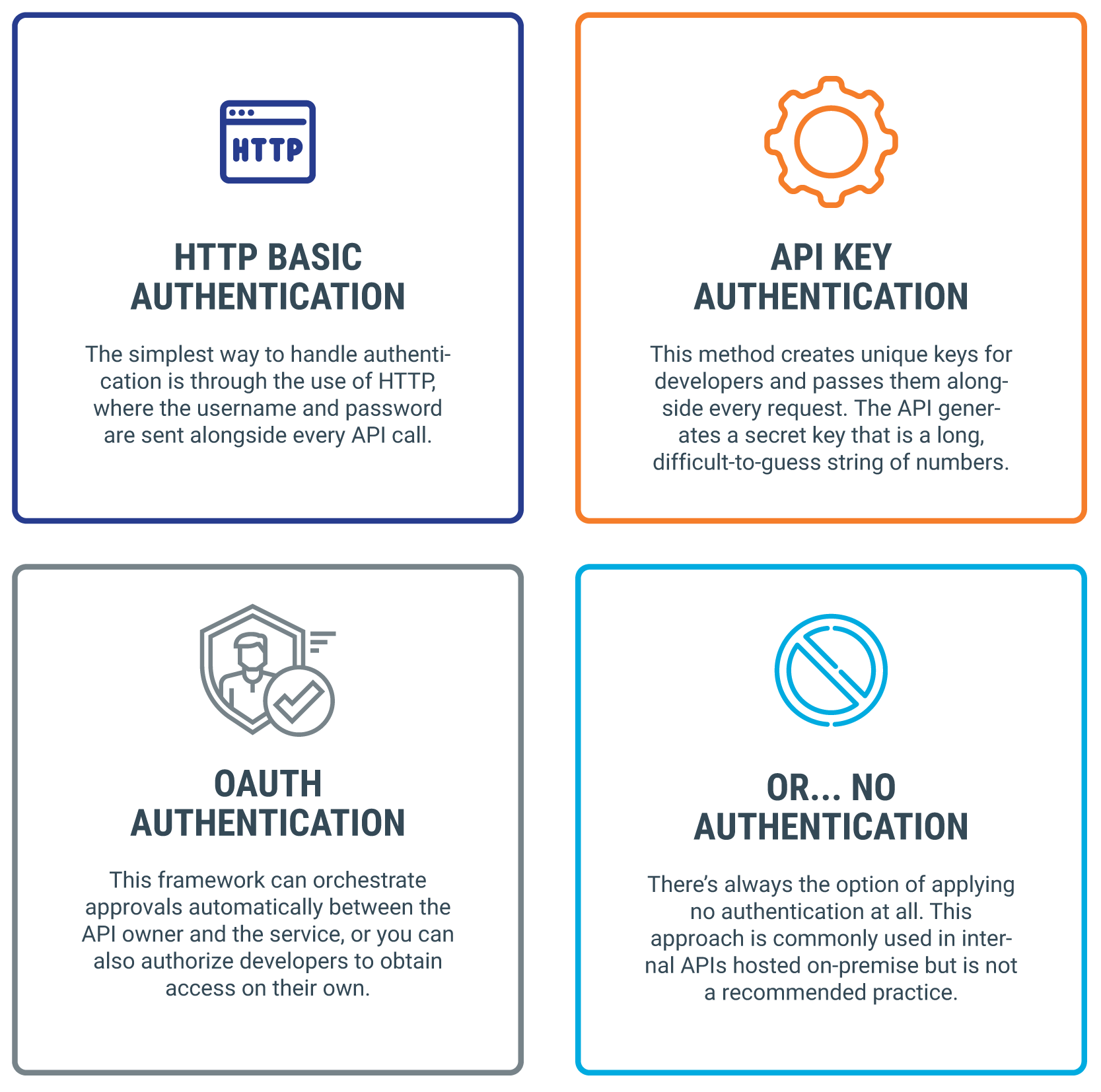
Most Popular API Authentication Methods 3Pillar Global
