Different Authentication Methods For Api are an enjoyable and interesting tool for children and grownups, offering a mix of education and learning and enjoyment. From coloring web pages and puzzles to mathematics challenges and word video games, these worksheets satisfy a large range of rate of interests and ages. They assist boost vital thinking, problem-solving, and creative thinking, making them suitable for homeschooling, class, or household activities.
Quickly accessible online, printable worksheets are a time-saving resource that can turn any type of day into an understanding journey. Whether you require rainy-day activities or supplementary discovering tools, these worksheets give unlimited opportunities for fun and education. Download and take pleasure in today!
Different Authentication Methods For Api
Different Authentication Methods For Api
Draw the structural formula and line bond for the following molecules Remember the following Carbons on the end of a chain are attached to three Question: Naming Alkanes - Worksheet #1 Name the following branched alkanes: HAC-CH- -CHE 1. сн. HC -CH-CH3 2. CH2 - CH3 HC-CH2-CH2-CH- -CH2 ...
Naming Alkanes Worksheet 1 Mr Lawson s Science Page
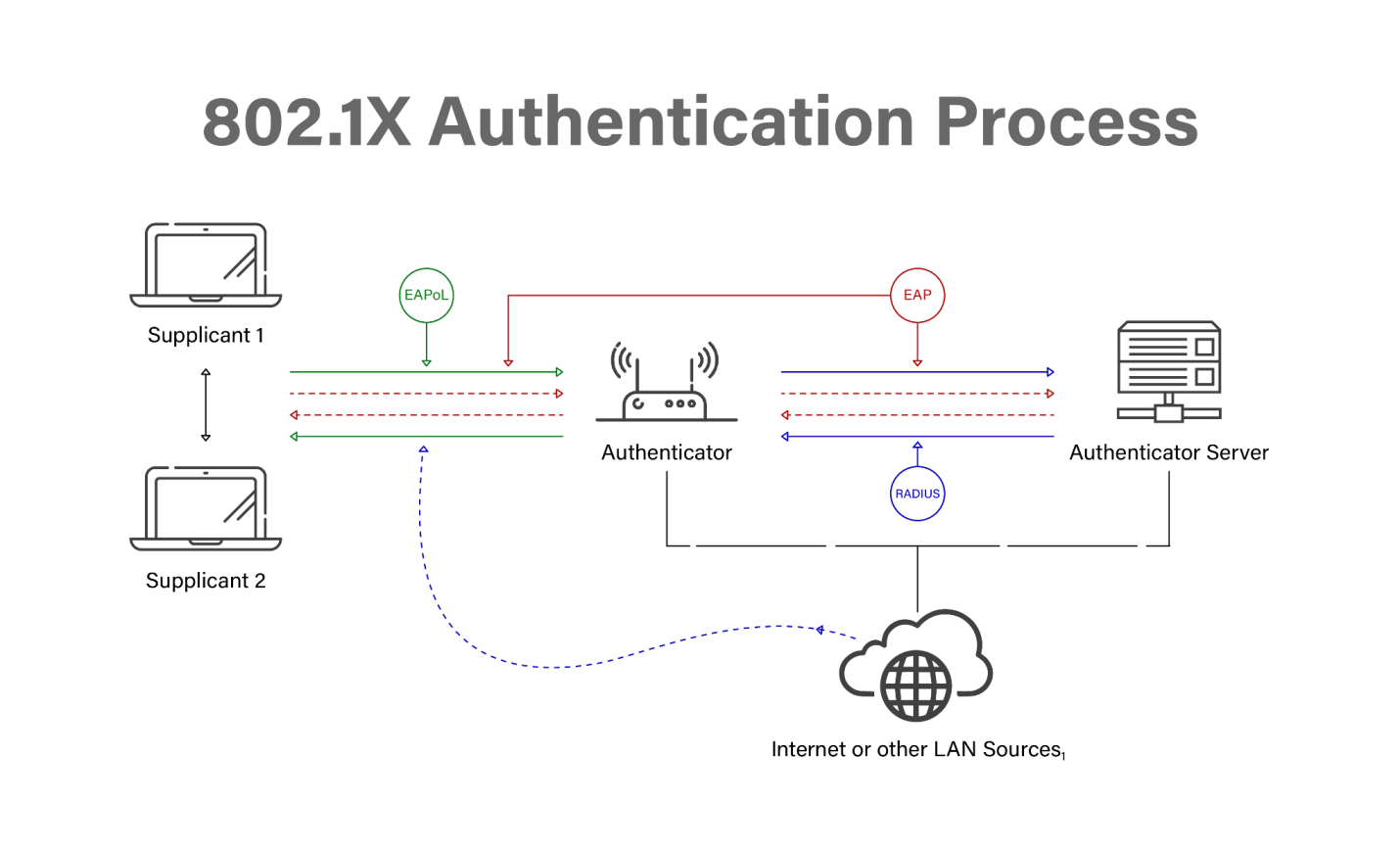
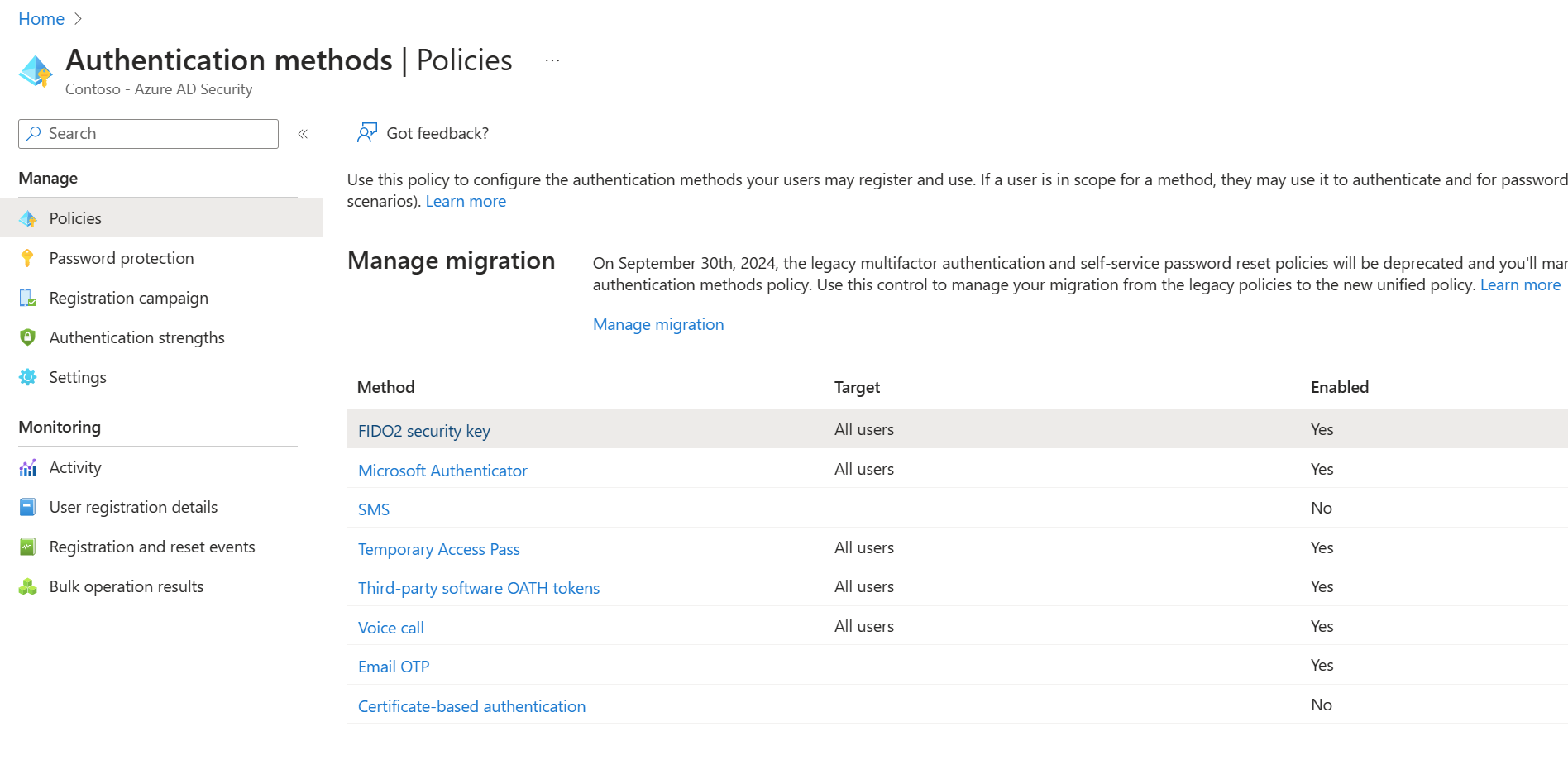
Load Authentication
Different Authentication Methods For ApiShare your videos with friends, family, and the world. Naming Alkanes Worksheet 1 Name the following branched alkanes H3C CH Naming Alkanes Worksheet 2 Draw the structural formula and line angle
Name the following branched alkanes: H.C-CH- CH CH H,C-CH CH CH,-CH H.C CH,-CH-CH-CH,-CH-CH CH-CH CHy-CH CH -CH,-сн, нс—сн ... IAM Authentication Methods Enterprise Security Securing APIs With Different Authentication Methods Inument
Worksheet 1 Name the following branched alkanes HAC CH

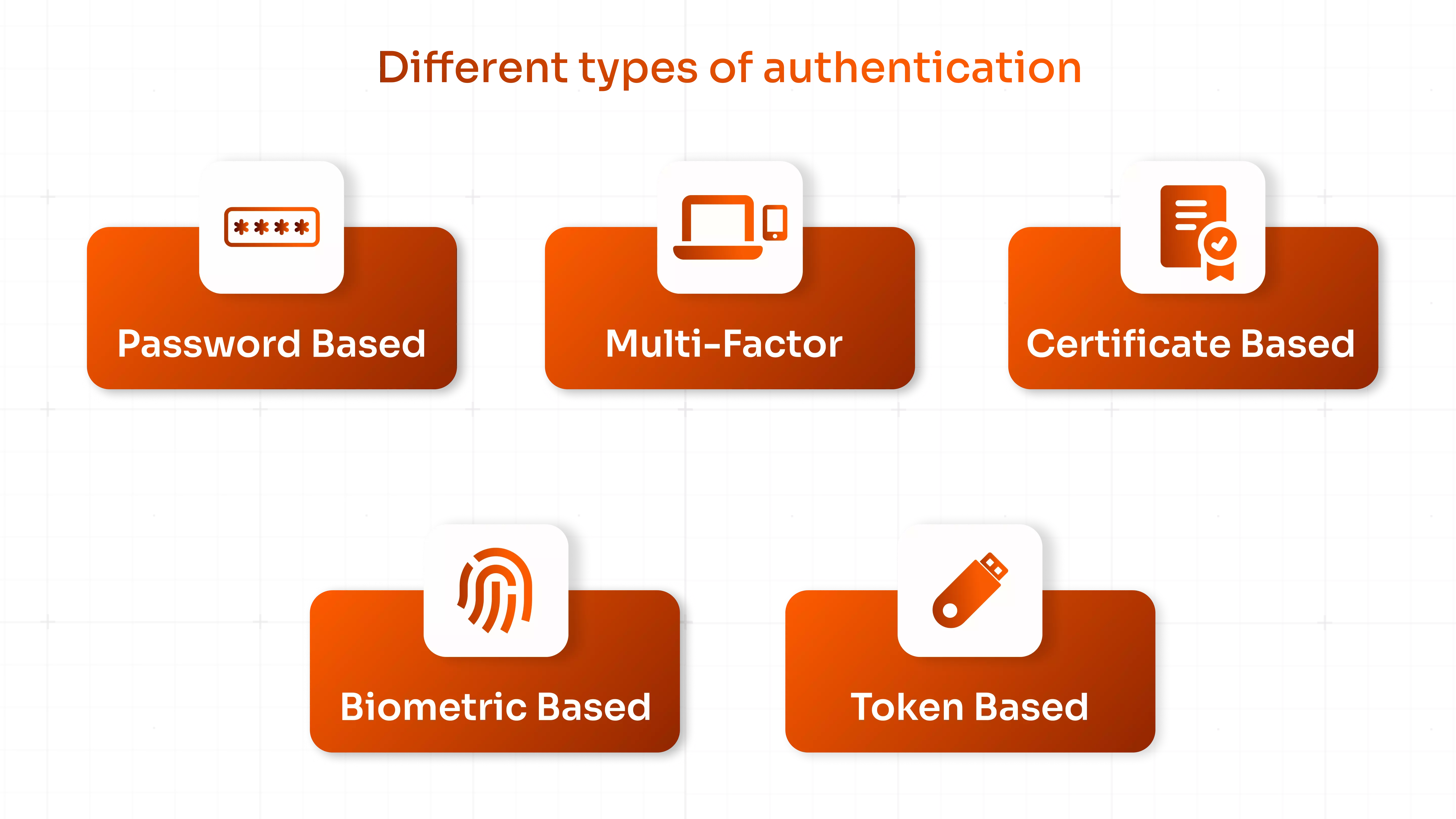
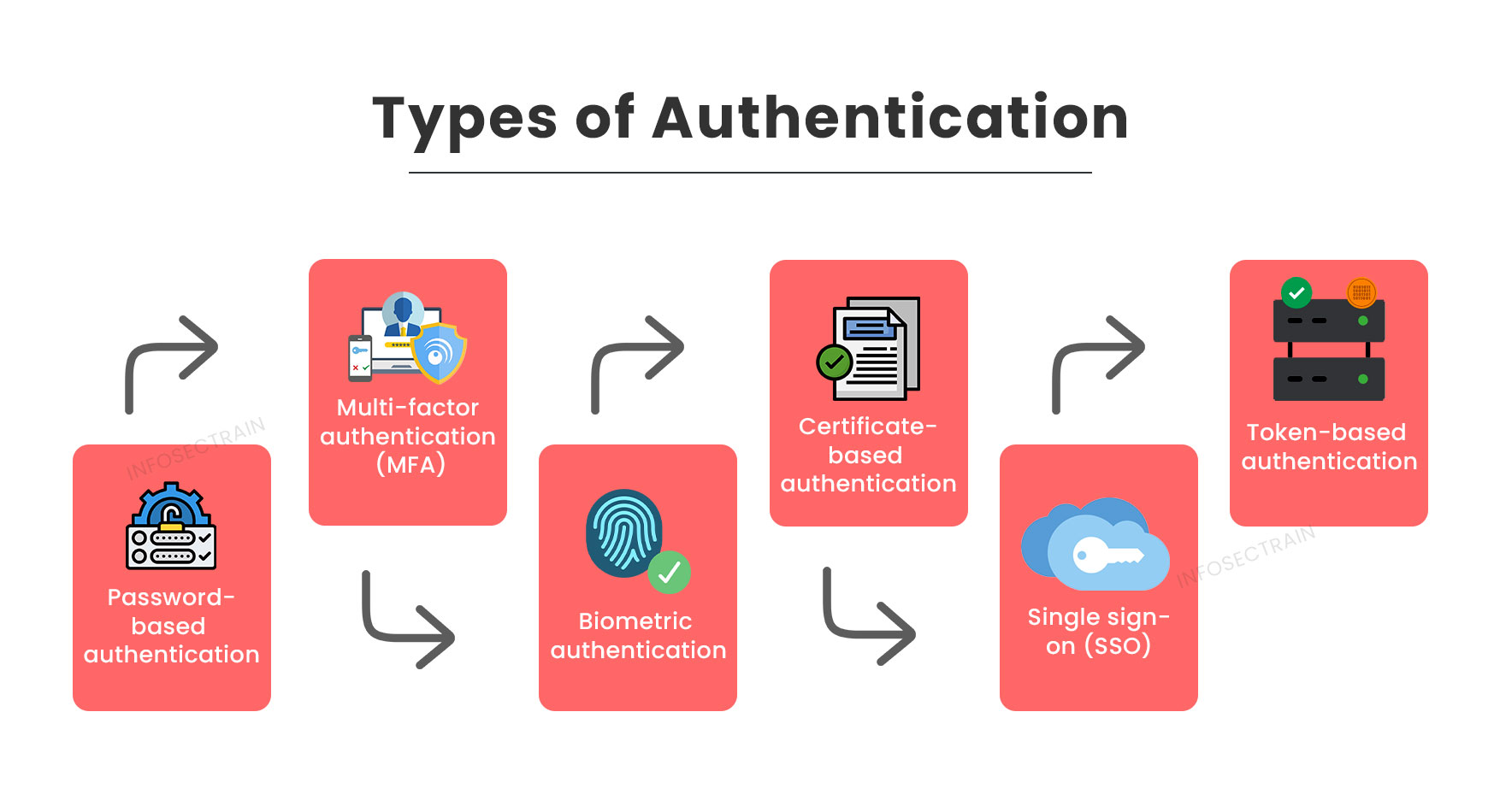
What Is Authentication Types Roles How It Works
Use the following steps to name an alkane 1 Find the main chain longest consecutive chain of C s Use the appropriate organic prefix for your root name 1 Authentication Vs Authorization
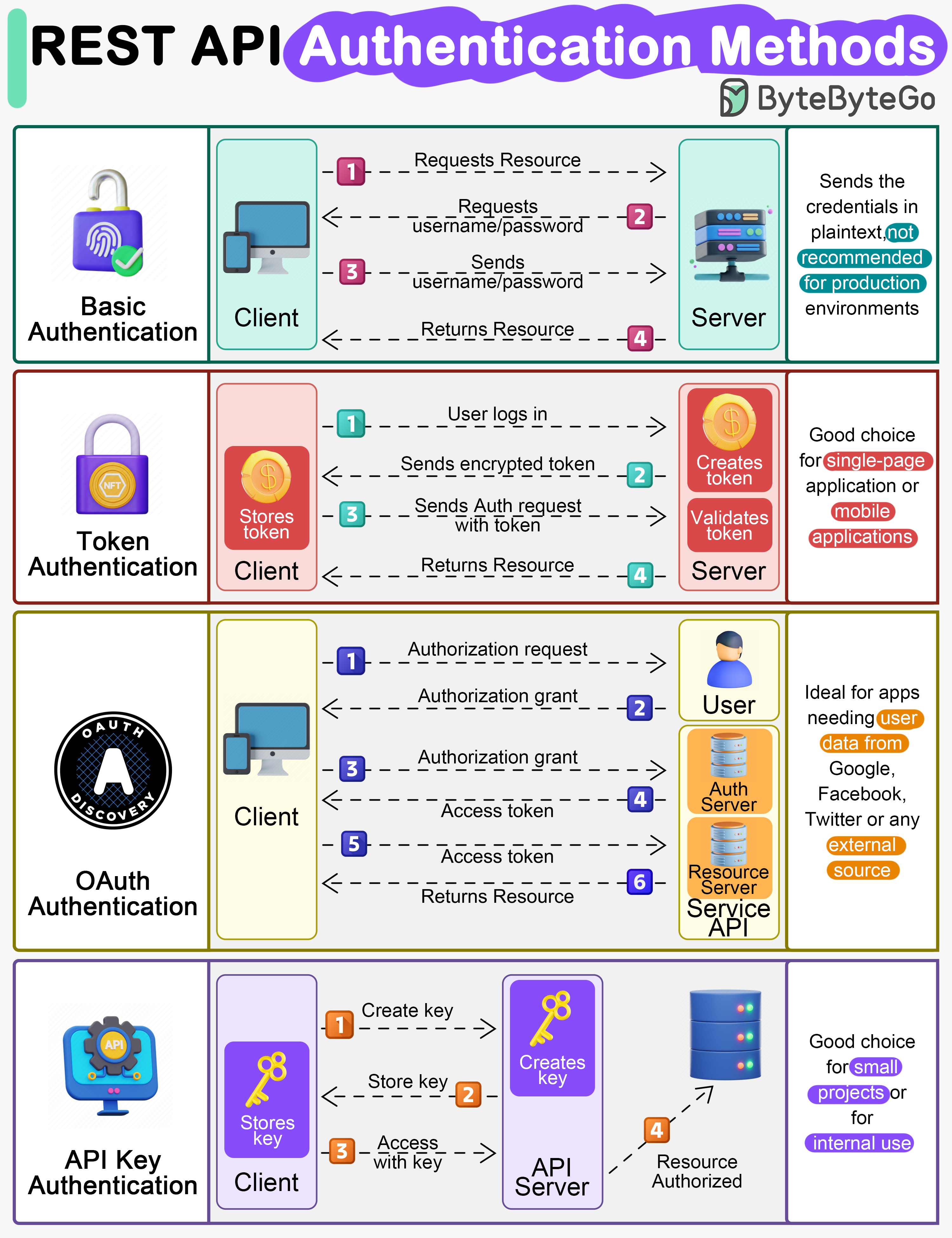
Name the following branched alkanes 1 H3C CH2 CH CH2 CH CH2 CH2 CH3 EP91 REST API Authentication Methods Most Popular API Authentication Methods 3Pillar Global

7 Authentication Methods To Secure Digital Access The Run Time

Authentication Vs Authorization
Authentication What Rivian s New Two Factor Authentication Means For

9 Popular API Authentication Methods To Secure API
Python Requests Library A Guide Datagy

Multi Factor Authentication MFA Explained
Microsoft Nps Authentication Methods Templates Sample Printables
Authentication Vs Authorization

Proxy Authentication Methods Explained

Securing APIs With Different Authentication Methods Inument